Implement single sign-on with Feide Open IdP
To understand how to integrate SAML federated access management, consider the following example of Feide open IdP authentication integrated with Squiz Content Management.
-
Ensure that SimpleSAMLphp is correctly installed on your Content Management system. Read the SAML account manager documentation for more information on this.
-
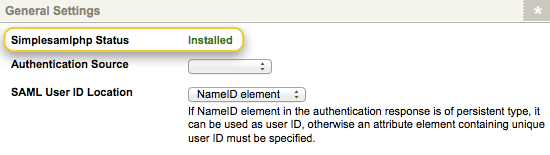
Create a SAML account manager asset. The SimpleSAMLphp status field should read installed. If SimpleSAMLphp is not installed, you will need to review the installation of SimpleSAMLphp on your system.
-
Provide import the metadata from the Feide identity provider. By default, the metadata for Feide identity provider is already included in the metadata distributed with SimpleSAMLphp. You can verify this by checking the saml20-idp-remote.php file on your SimpleSAMLphp installation within Squiz Content Management.
The Feide identify provider metadata required is available on Open IdP Feide and is as follows:$metadata['https://openidp.feide.no'] = array ( 'metadata-set' => 'saml20-idp-remote', 'entityid' => 'https://openidp.feide.no', 'SingleSignOnService' => 'https://openidp.feide.no/simplesaml/saml2/idp/SSOService.php', 'SingleLogoutService' => 'https://openidp.feide.no/simplesaml/saml2/idp/SingleLogoutService.php', 'certData' => 'MIICizCCAfQCCQCY8tKaMc0BMjANBgkqhkiG9w0BAQUFADCBiTELMAkGA1UEBhMCTk8xEjAQBgNVBAgTCVRyb25kaGVpbTEQMA4GA1UEChMHVU5JTkVUVDEOMAwGA1UECxMFRmVpZGUxGTAXBgNVBAMTEG9wZW5pZHAuZmVpZGUubm8xKTAnBgkqhkiG9w0BCQEWGmFuZHJlYXMuc29sYmVyZ0B1bmluZXR0Lm5vMB4XDTA4MDUwODA5MjI0OFoXDTM1MDkyMzA5MjI0OFowgYkxCzAJBgNVBAYTAk5PMRIwEAYDVQQIEwlUcm9uZGhlaW0xEDAOBgNVBAoTB1VOSU5FVFQxDjAMBgNVBAsTBUZlaWRlMRkwFwYDVQQDExBvcGVuaWRwLmZlaWRlLm5vMSkwJwYJKoZIhvcNAQkBFhphbmRyZWFzLnNvbGJlcmdAdW5pbmV0dC5ubzCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEAt8jLoqI1VTlxAZ2axiDIThWcAOXdu8KkVUWaN/SooO9O0QQ7KRUjSGKN9JK65AFRDXQkWPAu4HlnO4noYlFSLnYyDxI66LCr71x4lgFJjqLeAvB/GqBqFfIZ3YK/NrhnUqFwZu63nLrZjcUZxNaPjOOSRSDaXpv1kb5k3jOiSGECAwEAATANBgkqhkiG9w0BAQUFAAOBgQBQYj4cAafWaYfjBU2zi1ElwStIaJ5nyp/s/8B8SAPK2T79McMyccP3wSW13LHkmM1jwKe3ACFXBvqGQN0IbcH49hu0FKhYFM/GPDJcIHFBsiyMBXChpye9vBaTNEBCtU3KjjyG0hRT2mAQ9h+bkPmOvlEo/aH0xR68Z9hw4PF13w==', 'NameIDFormat' => 'urn:oasis:names:tc:SAML:2.0:nameid-format:transient', ); -
Register an account on the open IdP Feide site (https://openidp.feide.no/) and add a new service provider entity for integration with Squiz Content Management.
-
Supply the new service provider entity with the SAML 2.0 service provider metadata from the SAML account manager. To do this:
-
Insert the SAML account manager’s assertion consumer service and single logout sevice URLs in the corresponding endpoint fields in the SAML 2.0 tab of your service provider entity settings on the Open IdP Feide site. These URLs can be found on the Details screen of the SAML account manager.
-
Alternatively, you can add a new service provider entity directly from SAML 2.0 XML metadata. The XML metadata of the SAML account manager can be accessed through the service provider metadata download URL field on the Details screen.
-
-
Once both the service and identity provider metadata has been configured, the authentication source details of your Feide open IdP entity must be added on the SimpleSAMLphp installation.
-
In the
authsources.phpfield on your SimpleSAMLphp installation, add the following, replacing the EntityID attribute with the name of the entity created on the Feide identity provider:// Add Feide OpenIDO authentication details 'feide' => array( 'saml:SP', // The entity ID of this SP. // Can be NULL/unset, in which case an entity ID is generated based on the metadata URL. 'entityID' => 'myentityid', // The entity ID of the IdP this should SP should contact. // Can be NULL/unset, in which case the user will be shown a list of available IdPs. 'idp' => 'https://openidp.feide.no', // The URL to the discovery service. // Can be NULL/unset, in which case a builtin discovery service will be used. 'discoURL' => NULL, ), -
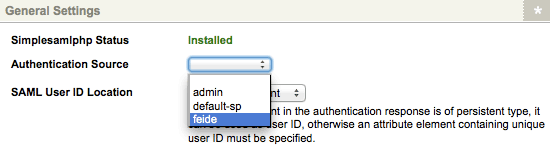
On the Details screen of the SAML account manager, the Feide entity will now be selectable in the authentication source field. Select this option.
-
In the SAML user ID location field, select the attribute element option, and then enter UID in the attribute element name field below. This will provide the SAML account manager with a unique ID for users requiring authentication.
-
your Content Management system has now been configured with federated access management with the Feide identity provider.
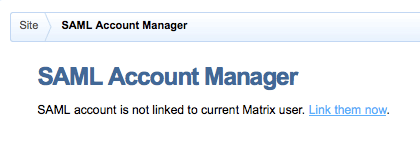
Preview the SAML account manager on the frontend to begin the authentication process. If you are logged into Squiz Content Management, you will be prompted to link your account; if you are not logged in, the user creation settings will be displayed.